Dotenv Vault vs HCP Vault
Dive into the features, experience, and other key factors to find your best fit in our comprehensive comparison of Dotenv Vault and HCP Vault.
As developers dealing with various kinds of data and information, we understand the importance of security in keeping our systems safe. With many things that can go wrong during data breaches (both for our business and our customers), it’s vital to prevent them from happening in the first place.
This makes choosing the right method for protecting our data essential, and it’s likely at the top of our list of concerns. It’s something we want to invest in, but the challenge lies in not knowing which tool is the perfect fit for us.
There are two popular options when it comes to selecting a secrets management tool - our very own Dotenv Vault and Hashicorp Vault. Both tools have their own advantages and disadvantages, making it difficult to decide which one is best for our needs. In this blog post, we’ll compare the two tools and help you make the ultimate choice:
Dotenv Vault vs HCP Vault: Overview
Starting with our own offering – Dotenv Vault, it’s a lightweight, user-friendly, yet powerful solution. As a relatively recent entry as a SaaS platform, it builds upon the best-in-class predecessor, setting the standard for handling environment variables. It’s a unified platform with no external dependencies, designed to extend the talents and capabilities of all developers.
On the other hand, Hashicorp Vault presents a more enterprise-focused solution that, while not as feature-rich, offers deeper integration with services across cloud providers. However, setting it up and getting started is comparatively more complex, making it better suited for vault brokers and professional cyber security teams.
So, which one stands out as the top alternative? To provide a better answer to this question, we will examine seven core factors that significantly influence the success of each tool:
- Core features
- Developer experience
- Supported integrations
- Deployment options
- GitHub activity
- Pricing and support
- Verdict
Dotenv Vault vs HCP Vault: Core features
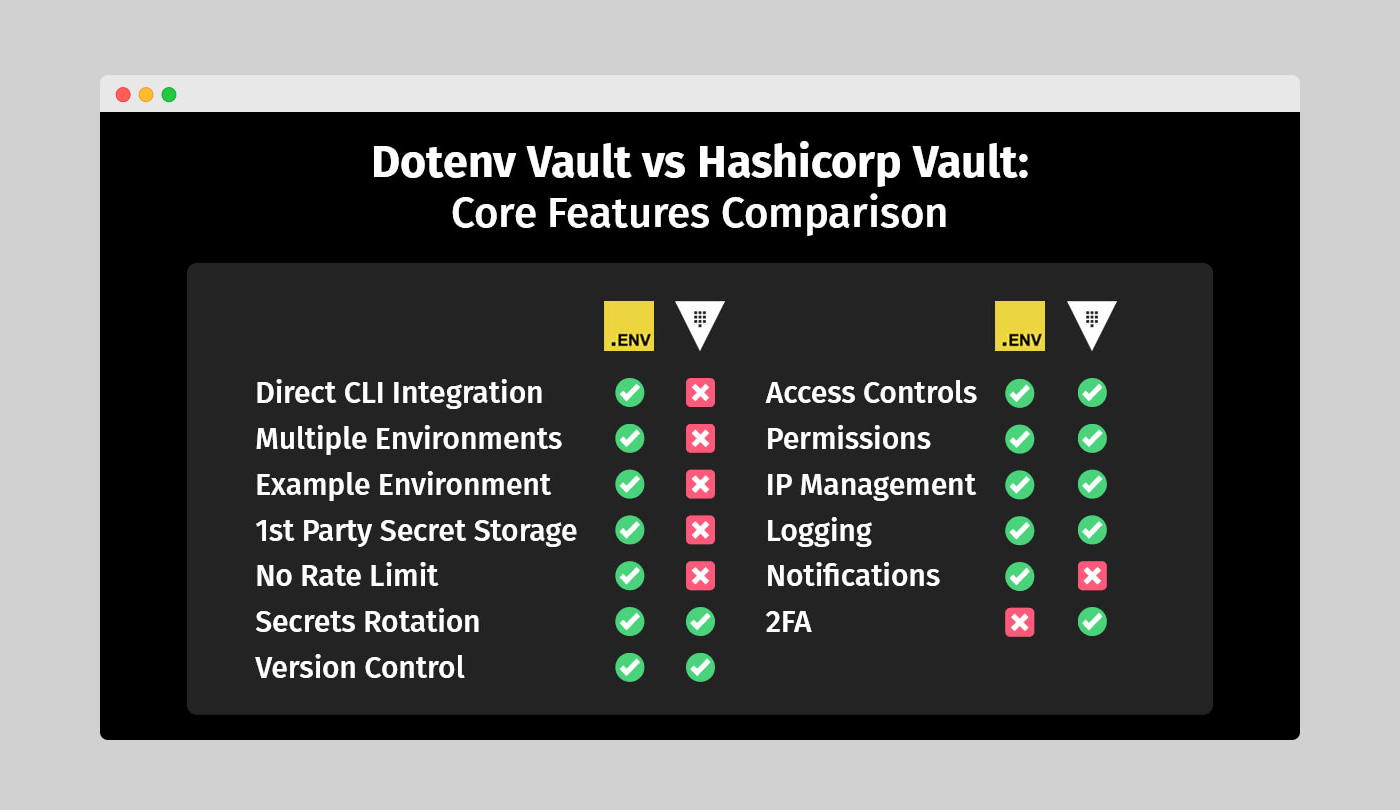
As the team behind Dotenv Vault, we’re excited to compare the core features of our solution with those of Hashicorp Vault. While there are similarities between the two, such as Versioning, Access Controls, Permissions, IP Management, and Logging, there are also key differences in each solution’s approach to structuring secrets, storage of secrets, and the presence of API limits.
In terms of security features, Hashicorp Vault offers some extras, like dynamic secrets and rotation, which are helpful for cloud provider integrations at scale. However, Dotenv Vault shines in its quality-of-life implementations, such as notifications for various secret interactions.
Figure 1: Dotenv Vault vs Hashicorp Vault - Core features comparison
Structural differences
If you’ve used other secret management solutions, you’re likely familiar with having multiple environments available. Our Dotenv Vault offers a familiar developer experience with secrets bound to environments like development, staging, and production, tying them into projects. In contrast, Hashicorp Vault uses clusters, which can lead to a long, difficult-to-manage list of clusters when working with multiple projects.
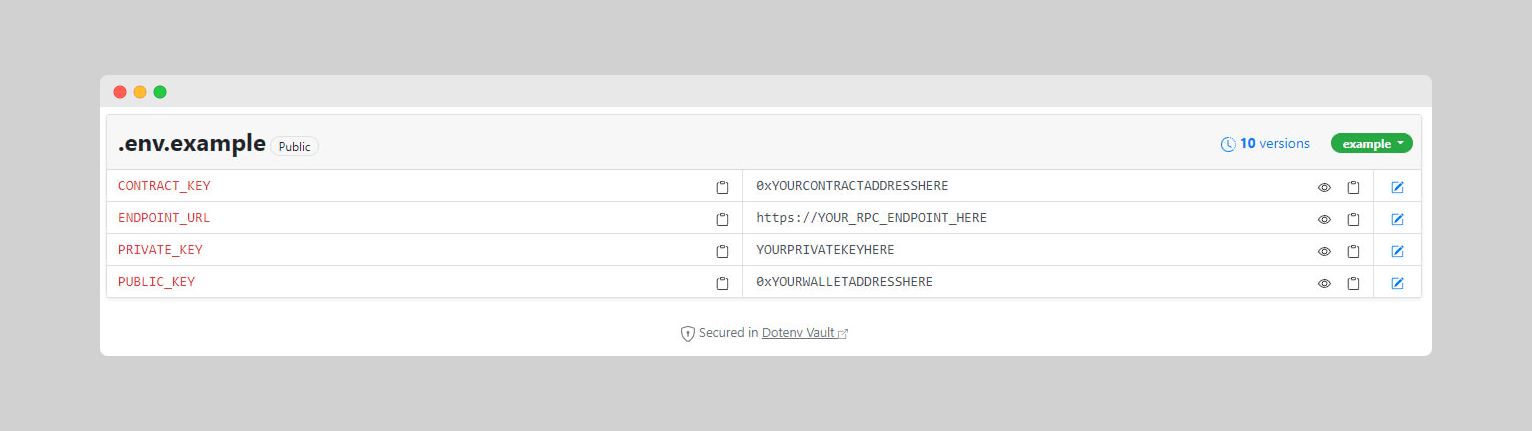
Our Dotenv Vault also offers an example environment, which is handy for creating tutorials or well-documented trails for other developers to follow. This public example environment allows you to set the format while keeping your actual secrets secure.
Figure 2: Dotenv Vault example environment in a Web3 setting
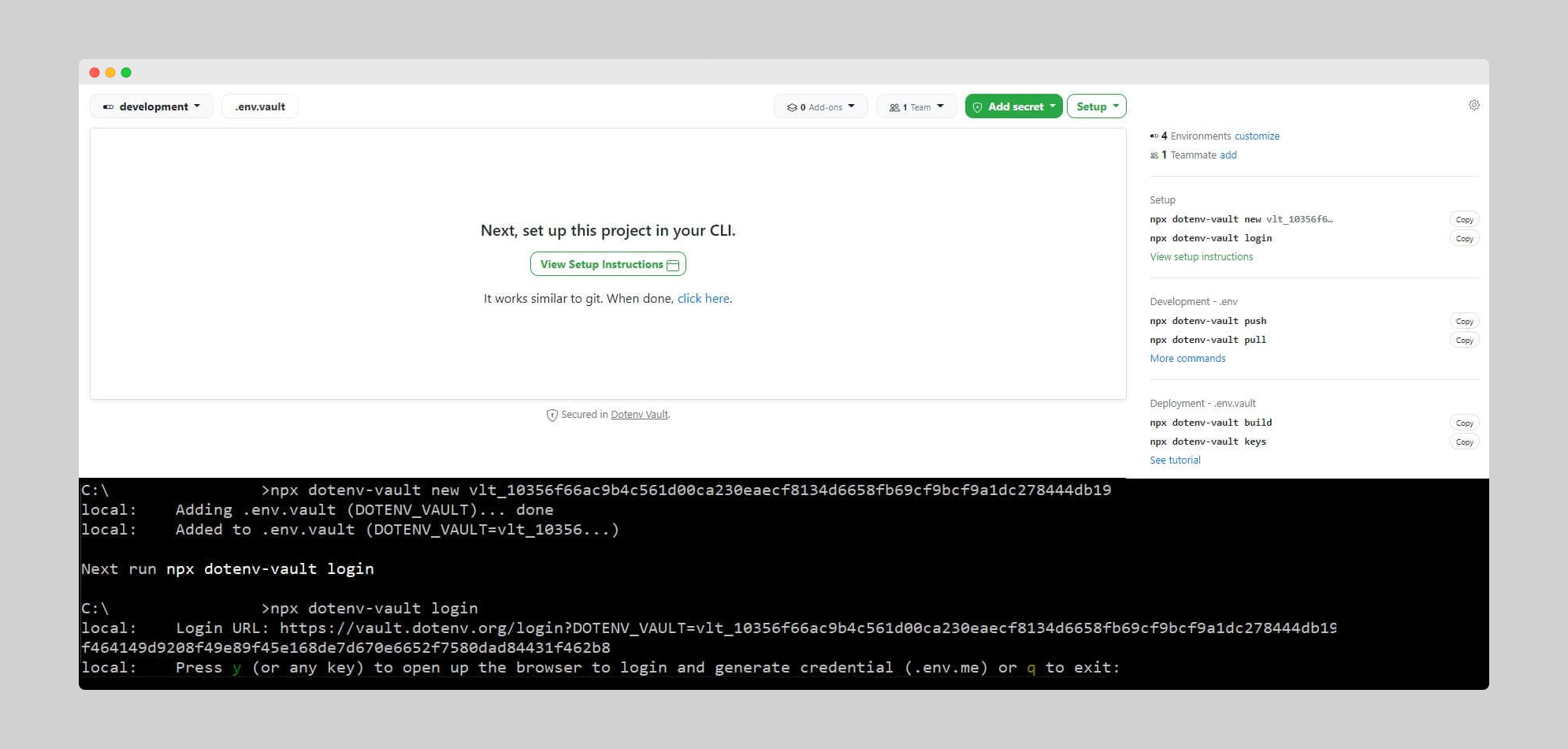
Direct CLI integration
We’re proud of how simple our Dotenv Vault CLI interactions are. With our package, you can run it without installation using npx, whereas the Hashicorp Vault CLI requires a download and setup before use. This results in better productivity and a smooth experience for dev teams.
Our recent [email protected] update introduced local build, decrypt, and keys commands, enabling developers to manage secrets independently of dotenv.org. This update also refined the build command, reducing nonce collisions and improving the overall developer experience.
From zero to hero
Dotenv Vault redefines simplicity, offering an incredibly straightforward setup process. With just two command-line inputs, configuring Dotenv Vault for your project is a breeze:
# Dotenv Vault CLI initialization
npx dotenv-vault new
npx dotenv-vault login
The streamlined setup of Dotenv Vault, condensed into two commands, prioritizes a fast and hassle-free experience. It is an excellent choice for developers seeking a seamless setup that enables them to quickly dive into their projects.
While HCP Vault also aims to provide a streamlined setup process for a smooth and efficient start, it does require two extra lines in your CLI to install required packages. This results in a total of four steps before initiating a fresh project:
# HCP Vault CLI initialization
brew tap hashicorp/tap
brew install hashicorp/tap/vault
vault login
vault operator init
When comparing the four-step setup of HCP Vault to Dotenv Vault, the process is generally just as unambiguous. However, Dotenv Vault holds a distinct advantage that sets it apart. Unlike HCP Vault, Dotenv Vault doesn’t necessitate any installation beforehand. Instead, you can effortlessly execute the package remotely using npx. This unique approach ensures a turbo-charged fresh start, making Dotenv Vault an enticing alternative for developers that have time and code efficiency as top priority.
Dynamic secrets and rotation
Both HCP Vault and Dotenv Vault offer valuable security features. HCP Vault provides dynamic secrets and proxied rotation capabilities, while Dotenv Vault enables rotation of the DOTENV_KEY for secure access. HCP Vault’s dynamic secrets generate secret values on-demand, preventing human errors related to app secrets. Its proxied rotation enforces automatic rotation within a specified timeframe, keeping services hidden from the public internet.
In comparison, our Dotenv Vault focuses on rotating the DOTENV_KEY to secure access to environment variables. Regularly updating this key reduces unauthorized access risk and helps maintain secret security. While not all languages and frameworks are supported, the list of compatible options is growing.
First party secret storage
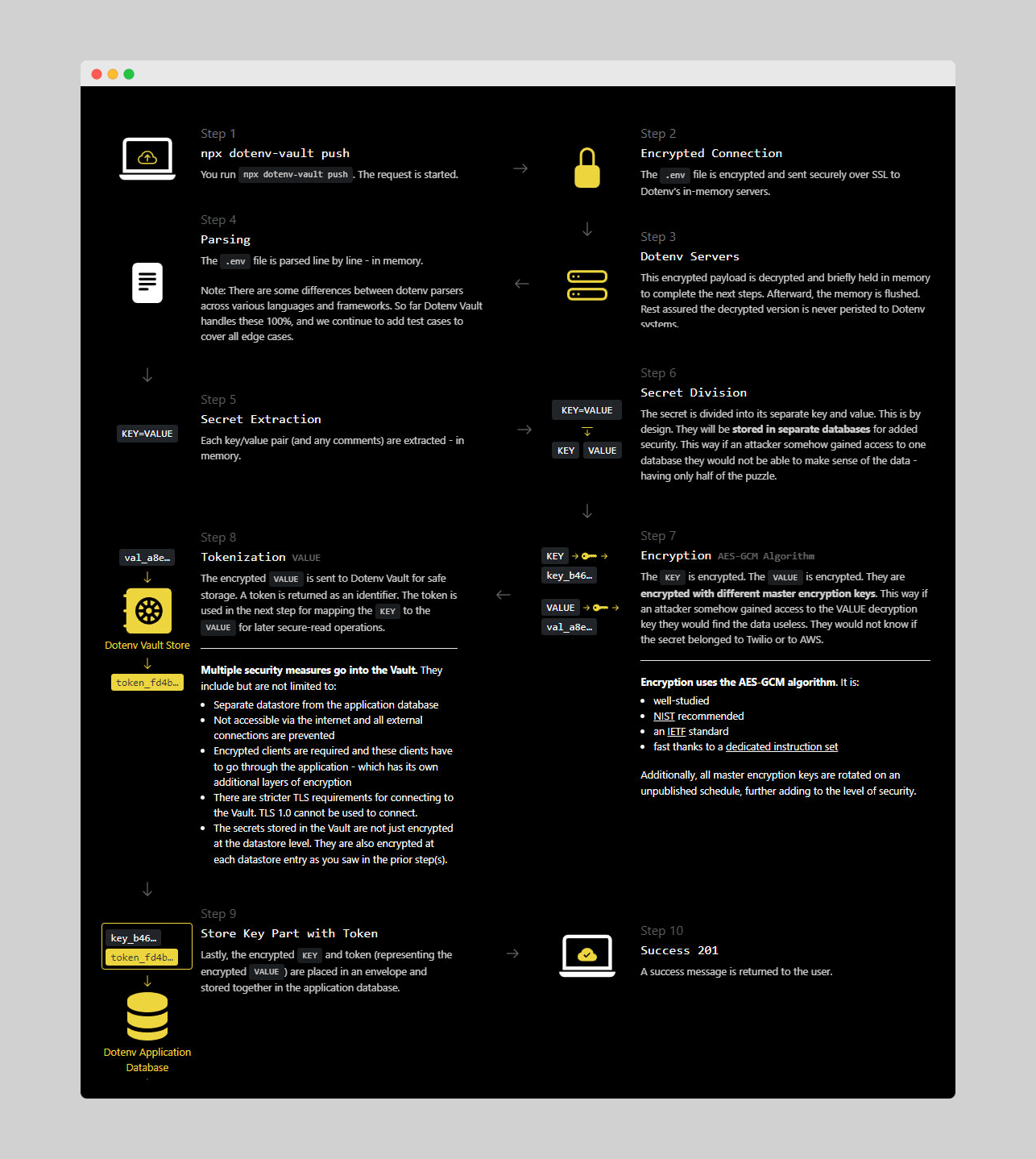
Unlike Dotenv Vault, Hashicorp Vault lacks first-party secret storage, offering only untrusted backend storage or alternative third-party options for enterprise customers. Our Dotenv Vault uses an in-house approach to handle users’ secrets, requiring no storage as the payload and decryption process are entirely in-memory. Once complete, the memory is flushed, eliminating any lasting unsecured presence on the servers.
This approach significantly hinders potential hackers, as there’s nothing left for them to steal in case of a breach. And to put things into even better perspective, here’s how Dotenv Vault’s workflow can be mapped out:
Figure 3: Dotenv Vault security overview
Rate limits & 2FA
Dotenv Vault offers unlimited API access, which is helpful for request-heavy implementations. Hashicorp Vault doesn’t provide this option, potentially requiring a plan upgrade for such applications.
However, Hashicorp Vault has an advantage when it comes to 2FA, which is essential for added security. We acknowledge this aspect and are continuously working to improve our offering to provide the best experience and security for our users.
Dotenv Vault vs HCP Vault: Developer experience
As the fellow developers like yourself, we understand that a great developer experience (DX) is just as crucial as the core feature sets of our tool. In this comparison, we’ll take a closer look at how Dotenv Vault and Hashicorp Vault stack up in terms of user-friendliness and accessibility for both newcomers and experienced developers.
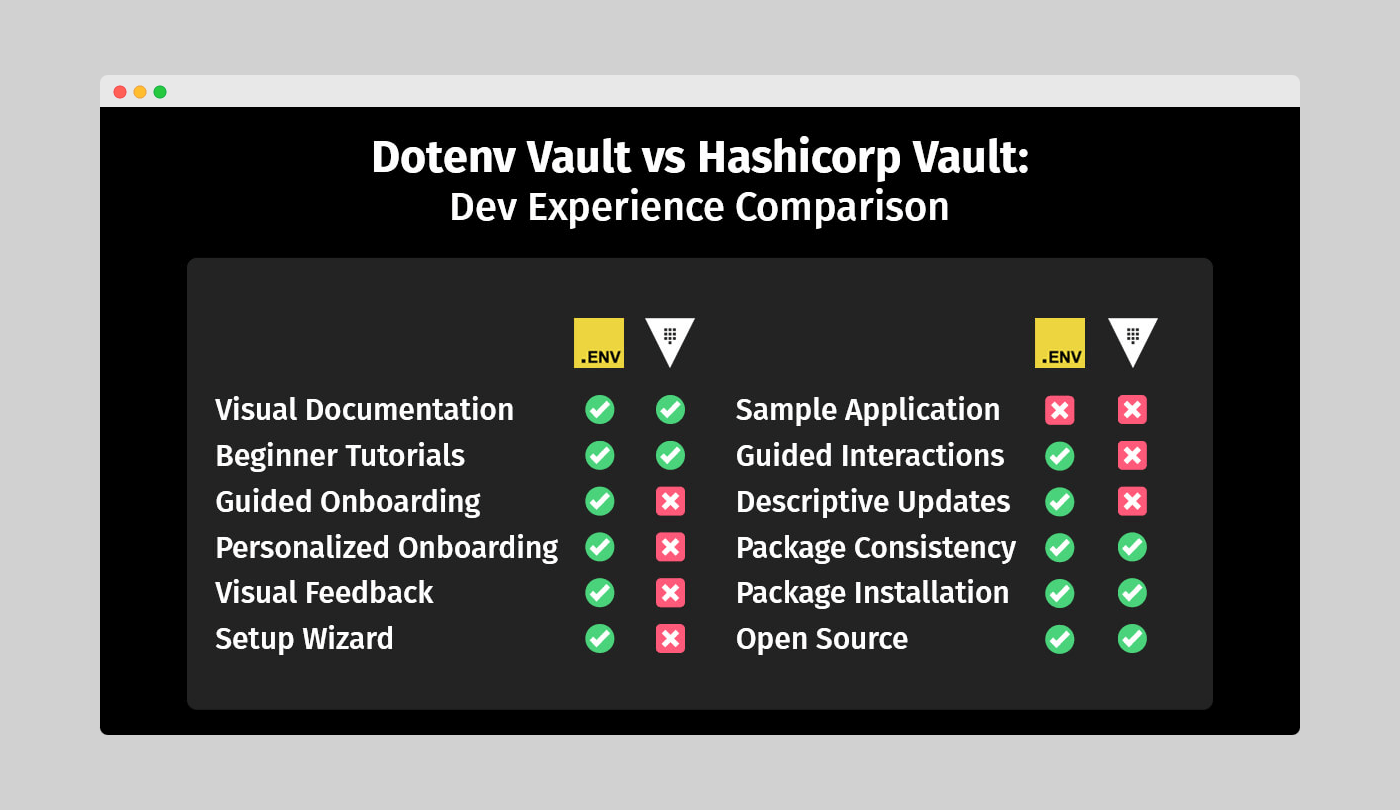
Here’s a quick overview of how well each tool fares in terms of developer experience according to some of the core aspects that comprise it:
Figure 4: Dotenv Vault vs Hashicorp Vault - Developer experience comparison
Onboarding, setup, and interactions
An excellent DX begins with the first interaction, which is why a well-structured onboarding process is essential. We’re proud that Dotenv Vault offers a guided and personalized onboarding experience that’s easy to pick up, while Hashicorp Vault falls short in this aspect.
Figure 5: Dotenv Vault guided setup process
Hashicorp Vault’s lack of visual feedback and guided interactions can make it challenging for new developers. In contrast, our Dotenv Vault provides relevant feedback in both the CLI and WebUI, making the workflow smoother. Our handy “Next-next-next” type of setup wizard also helps you initialize your app’s environment quickly and easily.
Tutorials and documentation
As a relatively new entry in the market, we admit that Dotenv Vault’s tutorials and documentation are still catching up with Hashicorp Vault’s extensive resources, including getting started guides, detailed tutorials, and a certification track. We’re working hard to improve our documentation and offer more resources for our users.
However, when it comes to changelogs and readme updates, we believe that our detailed and accessible overviews of each commit make it easier for developers to understand how our solution works. This approach also improves the overall security of Dotenv Vault by making it easier for auditors to evaluate safety and identify areas for improvement.
Changelogs and readme files
When it comes to the comprehensiveness of each changelog and readme update, our approach offers a much more accessible entry for developers looking to better understand how it functions. In contrast to Hashicorp’s solution, Dotenv Vault includes detailed overviews of each commit, which are both accessible and straightforward, and effectively eliminate unnecessary obstacles before potential contributors.
Looking at the commit history, it is easy to notice this fundamental difference. Every changelog features nothing more than a version update, leaving you entirely on your own, while comparing the differences in the code segments. Even if Hashicorp Vault is open source like our very own Dotenv Vault, the real winner in this vertical and the tool that follows in the footsteps of this approach more closely is by far the latter. And as a side benefit, this also improves the overall security of the solution by making it much easier for auditors to evaluate the safety and identify weak points for further improvement.
Package installation and consistency
In terms of package consistency, both solutions perform similarly. However, Dotenv Vault has the advantage of not requiring installation, unlike Hashicorp Vault. The installation process for both tools is consistent across different operating systems, which is beneficial for cross-platform administrators.
Our Dotenv Vault’s familiar workflow for developers accustomed to working with git and GitHub simplifies the learning curve. We also cater to various platforms by offering Windows executable installation through 32-bit and 64-bit installers and Homebrew installation for macOS users. This versatility makes Dotenv Vault even more appealing to developers working on different systems.
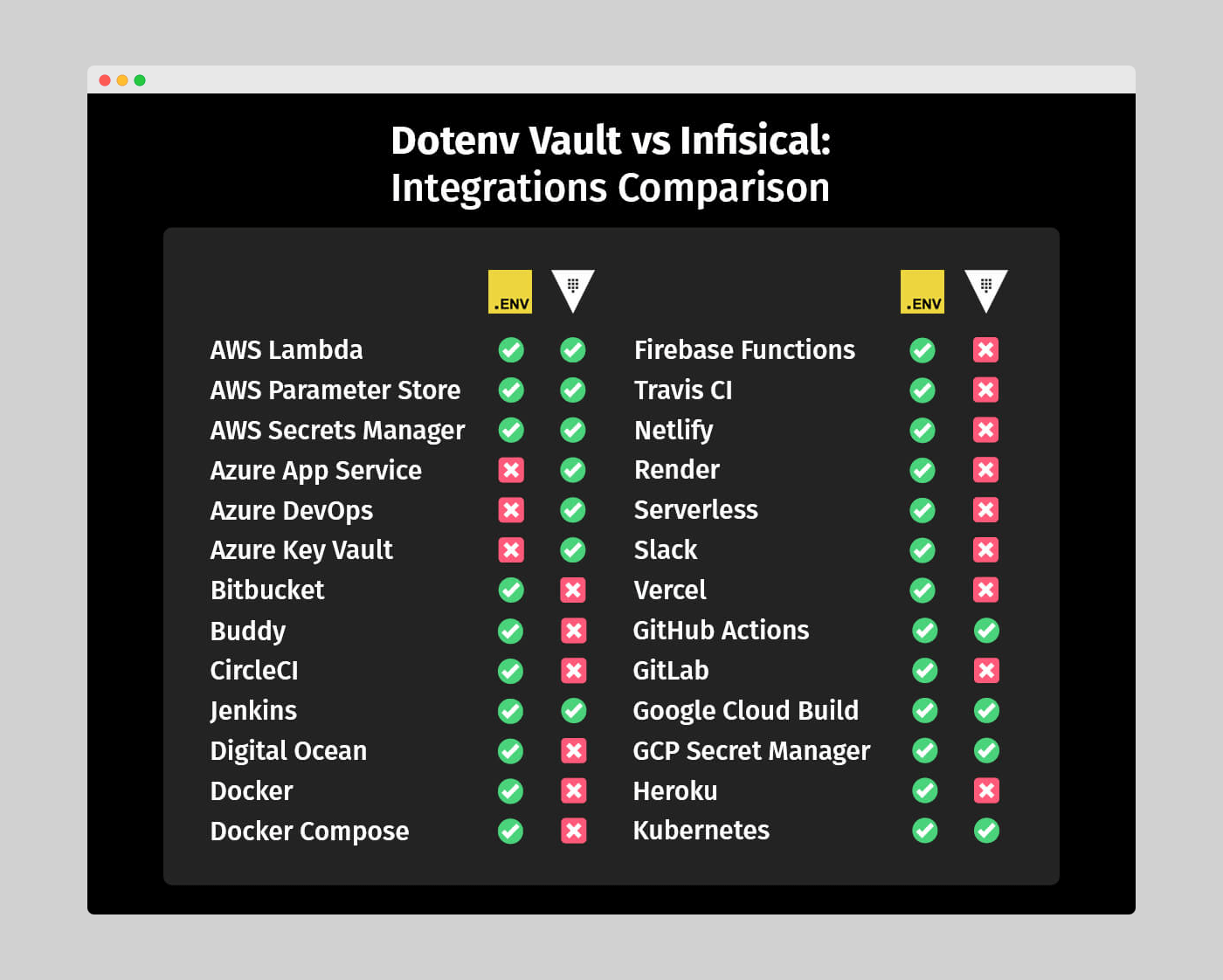
Dotenv Vault vs HCP Vault: Supported integrations
At Dotenv, we know that integrations play a crucial role in a tool’s usefulness. While Hashicorp Vault’s list of integrations initially appears extensive, most of them are designed for their other tools, such as Terraform. Only a small portion applies to their Vault implementation.
Hashicorp Vault aims to capture a larger share of the cloud provider market, which is why it supports not just AWS, Azure, and Google, but also Alibaba, Tencent, and OVH clouds. Meanwhile, we’ve focused on integrations most helpful to the majority of developers, such as CircleCI, Digital Ocean, Heroku, and Vercel. However, Hashicorp Vault does offer some interesting alternatives like MongoDB and Kubernetes, broadening its reach.
Figure 6: Dotenv Vault vs Hashicorp Vault – Supported integrations comparison
Addon and plugin integration
We understand the importance of seamless integration with popular tools and platforms. That’s why Dotenv Vault offers a GitHub Add-on and a VSCode extension with Rust support. In comparison, HCP Vault ensures a versatile developer experience with its compatibility with GitHub and a VSCode extension.
Our GitHub Add-on automatically builds encrypted .env.vault files when secrets change, keeping your projects up-to-date and synchronized. Our VSCode extension with Rust support also expands our adaptability across different programming languages and development environments.
HCP Vault, too, focuses on addon and plugin integration, offering compatibility with GitHub and a VSCode extension for managing secrets within developers’ preferred settings.
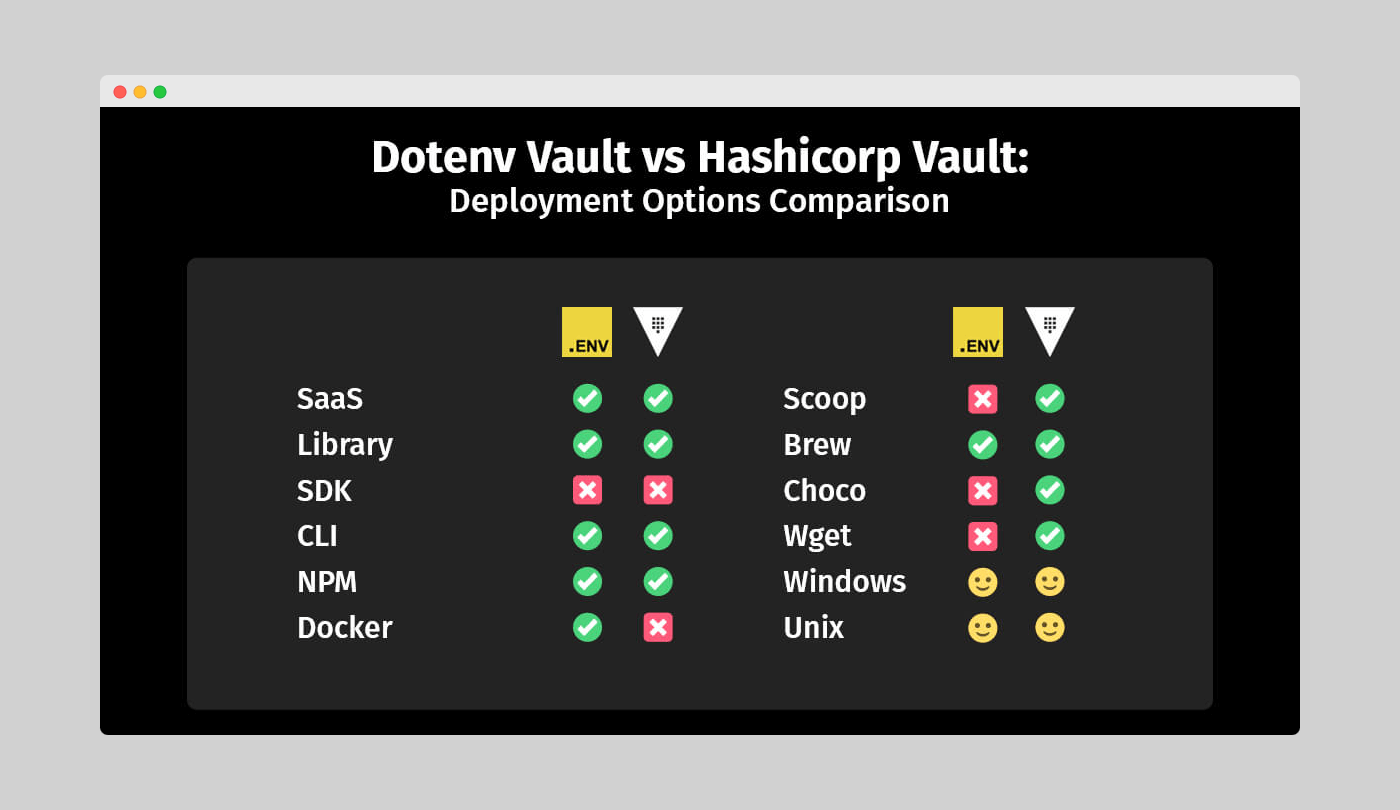
Dotenv Vault vs HCP Vault: Deployment options
Both Dotenv Vault and Hashicorp Vault have similarities in deployment options, thanks to their open-source nature. As SaaS platforms, they offer official libraries and community-led initiatives to support various languages. Hashicorp stands out with its Powershell implementation, while we cater to Docker and .net users.
The significant degree of interoperability between both tools ensures a pleasant experience across programming languages.
Figure 7: Dotenv Vault vs Hashicorp Vault – Deployment options comparison
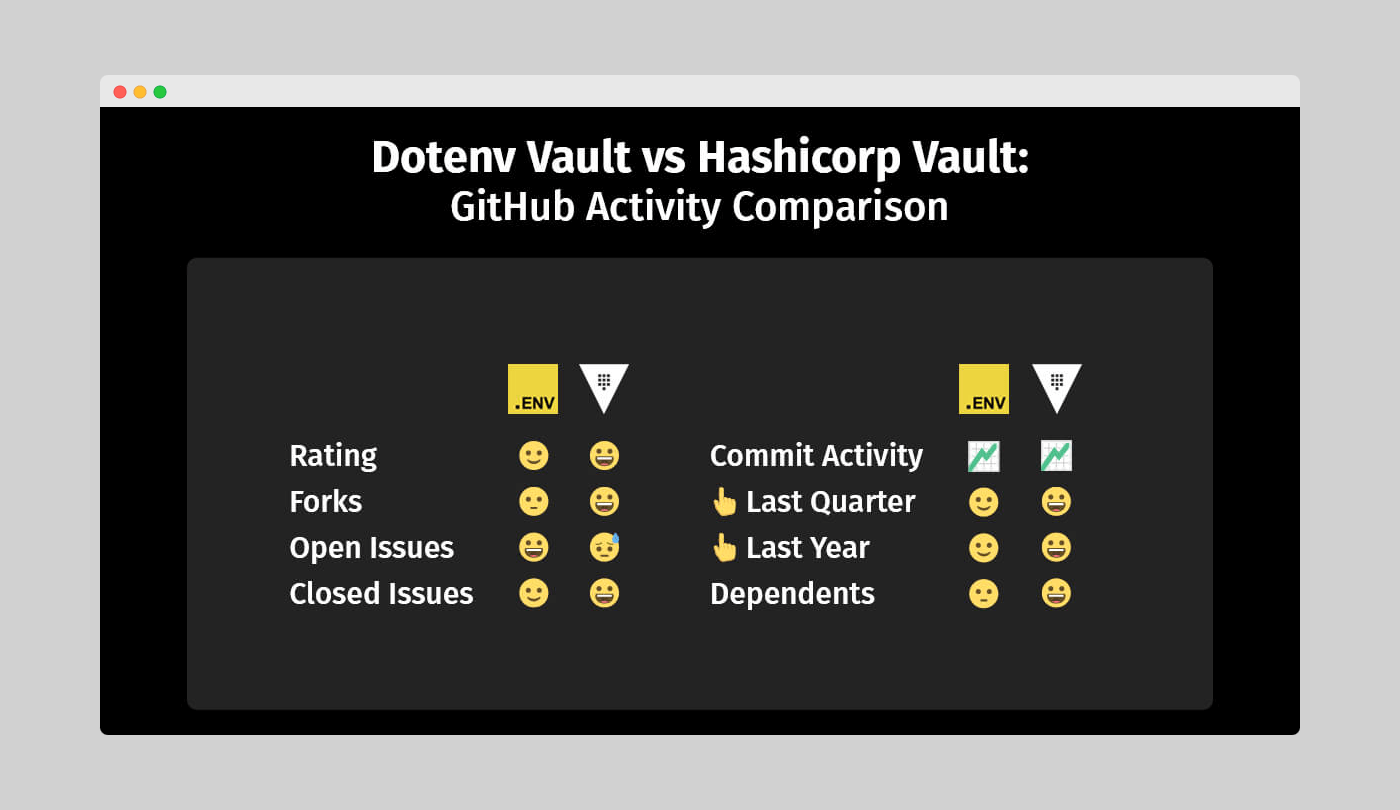
Dotenv Vault vs HCP Vault: GitHub activity
Hashicorp Vault’s longer market presence is evident in its GitHub activity. While we’ve made a noticeable impact despite our shorter tenure, Hashicorp Vault has more pronounced community participation.
Hashicorp’s repo boasts a higher star rating, a larger number of forks, and more issues listed on the platform. However, when comparing the ratio of open to closed issues, we seem to have an edge. This could be due to sample sizes or faster issue resolution for Dotenv Vault.
In terms of commit activity, our commitment appears to increase over time, while Hashicorp’s remains stable. This suggests that Hashicorp Vault has a healthy and consistent development cycle, while our increasing contributions may benefit Dotenv Vault in the long run.
Figure 8: Dotenv Vault vs Hashicorp Vault – GitHub activity comparison
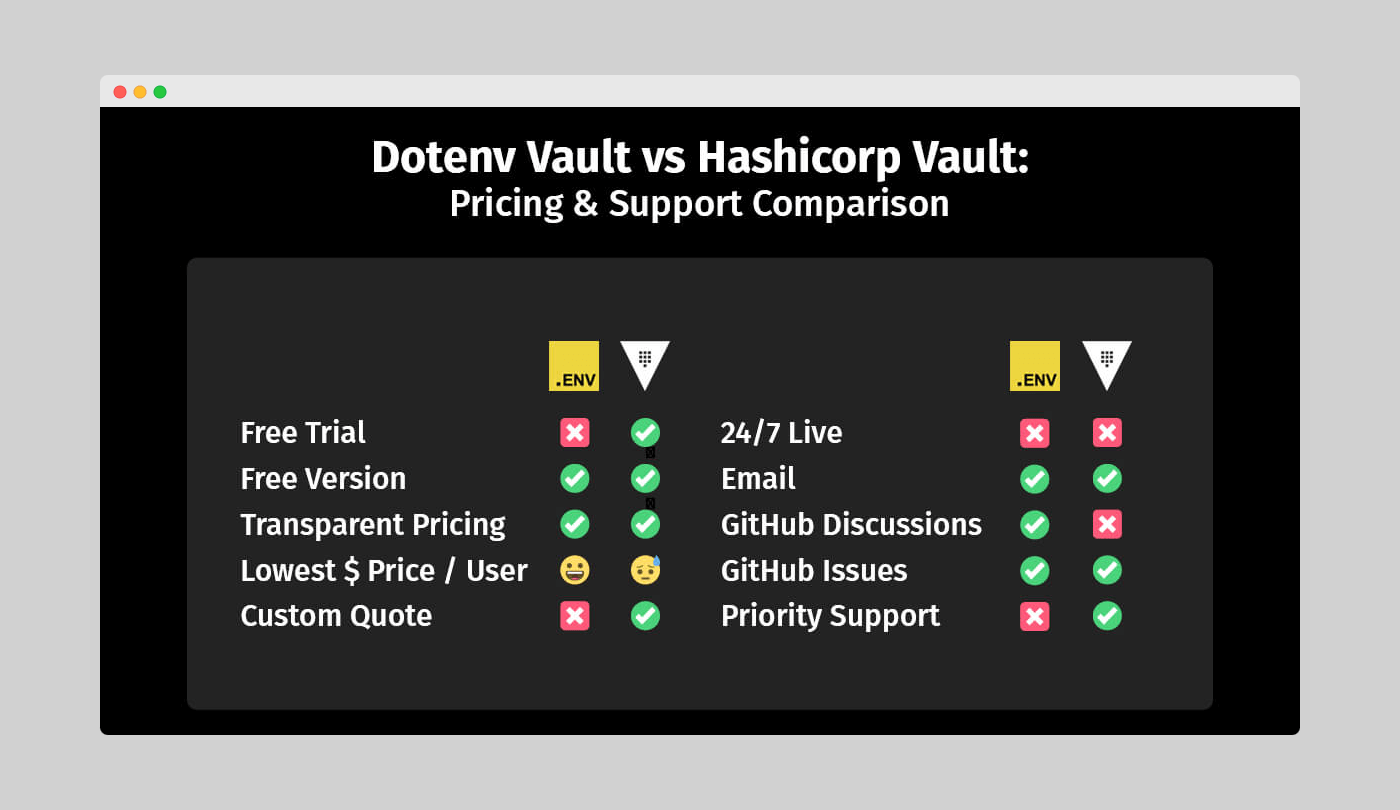
Dotenv Vault vs HCP Vault: Pricing and support
In this crucial category of pricing and support, we, the Dotenv Vault team, want to highlight some significant differences between our solution and Hashicorp Vault. Each tool takes a different approach to pricing, and while neither is inherently better, they cater to specific use cases.
Figure 9: Dotenv Vault vs Hashicorp Vault – Pricing and support comparison
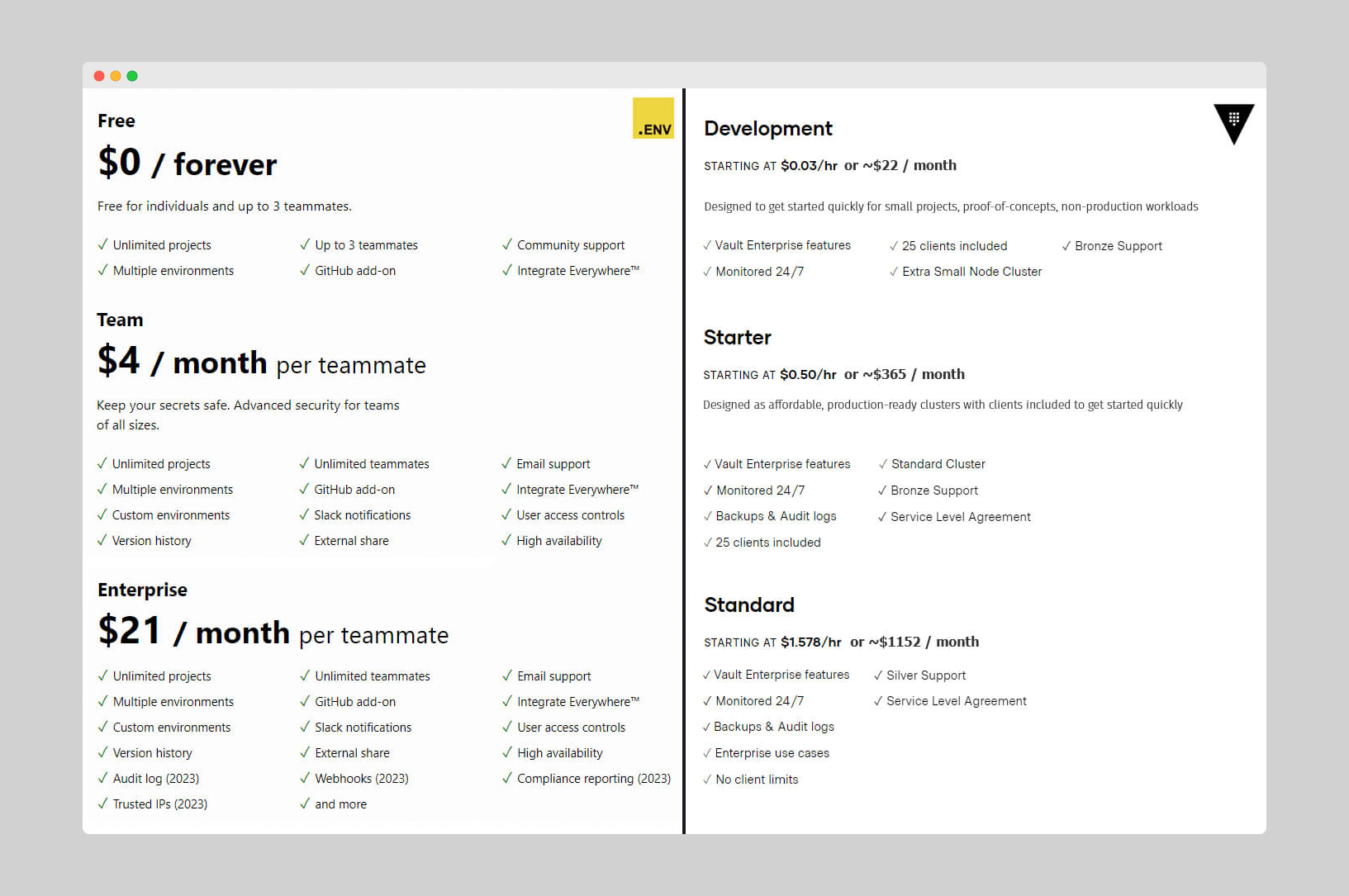
We’ve chosen a traditional SaaS-based pricing model for Dotenv Vault, with tiers on a per-user basis. Hashicorp Vault, on the other hand, uses a per-hour quote similar to cloud providers like Digital Ocean. This pricing model aligns with their focus on cloud provider integrations, while our per-user pricing approach better suits developers and teams.
Beyond the pricing models
Besides the distinct pricing models, both solutions share some similarities. We’re proud that both Dotenv Vault and Hashicorp Vault offer free versions, transparent plan tier breakdowns, and custom quotes for non-standard implementations.
Hashicorp Vault provides a free trial, but our free version is feature-complete, making a trial unnecessary. Interestingly, the non-SaaS version of Hashicorp’s tool is entirely free but lacks the assistance offered by the paid Web-based alternative, making it most useful for experienced Hashicorp users.
Figure 10: Dotenv Vault vs Doppler - Pricing plans comparison
Support options overview
As popular developer SaaS solutions, both tools benefit from community support, boosting their GitHub activity. One difference is that we offer an additional channel for community support – GitHub Discussions, which may lead to better interactions between contributors and those seeking help.
In terms of other support channels, Hashicorp Vault has a ticketing system run by a dedicated support team, offering more security than our email support option. Hashicorp’s remote assistance sessions also stand out in priority support.
Dotenv Vault vs HCP Vault: Verdict
We hope that this comparison helps you understand the similarities and differences between Dotenv Vault and Hashicorp Vault. The best choice depends on your specific needs and the systems you plan to use in your development process.
If you’re looking for an effective and user-friendly way to manage environment variables for your development team, Dotenv Vault is an excellent choice. However, if you’re an experienced developer seeking deeper integrations with various cloud providers beyond the common ones, Hashicorp Vault may be more suitable, provided you can accommodate the per-hour pricing model and a less intuitive interface. Ultimately, your needs will guide your final decision.